Tor hygiene
Download Tor Browser directly from the project site, not from a mirror. Verify the download signature with GnuPG. Set security to "Safest" — Nexus doesn't need JavaScript to load.
Nexus has one of the most copied interfaces on the darknet. Phishing clones rotate weekly. This page lists the four real .onion addresses, cross-checked against PGP-signed announcements on Dread. Copy, don't type. One wrong character leads somewhere else entirely.
Nexus launched in November 2023. Within fourteen months it had 47,000 active accounts and a reputation for the best-looking interface in the darknet marketplace ecosystem — hot pink, cyan, deep purple, the whole cyberpunk mood board.
That design is the problem. It's also why you're on this page.
A marketplace that visually distinct invites copycats. Phishing operators scrape the CSS, spin up their own .onion, change only the address and the wallet receivers, and wait for people to type the URL from memory. They look identical. They behave identical — until you deposit Monero and realise the withdrawal button does nothing.
Our directory exists to solve a narrow problem. Not "what's the best market." Not "is darknet safe." Just: given that you already want to reach Nexus, which of the 40+ .onion addresses floating around forum threads and Google-indexed scraper sites is the one Nexus administrators actually operate?
We answer that by cross-referencing four sources. The admin PGP signature posted on Dread. The canonical domain listed in Nexus's own in-app announcements. The descriptor returned by the Tor directory authority. And the handshake fingerprint of the landing page itself. If all four line up, the address is on this page. If one fails, it isn't.
"Every phishing site we've catalogued had the CSS exactly right. The .onion was always wrong. The gap between those two facts is where wallets empty."
— Dread user /u/node_watcher, thread archive, March 2026
The address on this page is not a shortcut around the verification you should do yourself. It's a shortcut past the first layer of obvious scams. Before you enter credentials, check the .onion character-by-character against the signed announcement. Bookmark it. Never reach Nexus through a search engine. Never follow a link someone DMs you on a forum.
Nexus isn't perfect. The company that runs it is anonymous. The escrow, while multisig and technically sound, still depends on a third key you don't control. Previous markets with nearly identical architecture have gone dormant with user funds still deposited. None of that is unique to Nexus. All of it applies to every centralised darknet marketplace currently operating.
What Nexus does well: Monero support as a first-class citizen, not a bolted-on afterthought. PGP login that works without a password. An interface that feels designed rather than assembled. An uptime record, 98.1%, that outperforms most of its peers.
What it doesn't: solve the fundamental problem of trusting a pseudonymous operator with your escrow. No marketplace solves that. Only minimising the time your funds sit on-platform does. Deposit, transact, withdraw. Treat the wallet like a hot stove.
Nexus runs four .onion mirrors because single-address architecture dies the first time a DDoS wave hits. When one mirror goes offline, traffic routes to the other three. Same database, same accounts, same balances. You can log in on NODE-02 and see the order you placed on NODE-01. The four addresses are not different marketplaces — they're four front doors into the same building.
The addresses rotate occasionally. Operators generate new key pairs when an old one becomes too widely phished, publish the new address through a signed Dread post, and deprecate the old one over a two-week window. That's why a link that worked in August 2024 might not work today. Our directory tracks the current set. If you bookmarked an address more than six months ago, check it against the codes on this page before you log in.
It's for people who have already decided to use Nexus and want to reach the real one instead of a phishing copy. It's for existing users who lost their bookmark. It's for vendors who need to verify a mirror is canonical before pointing customers at it.
It isn't a recruitment pitch. It isn't advice to start using a darknet market. Participation carries legal risk in most jurisdictions. What we do is harm reduction for people whose decision is already made — better the real address than a phishing clone that empties wallets and ruins weeks.
Most wallets lost on Nexus are lost before the market even loads. The failure points are Tor hygiene, PGP setup, and wallet discipline. Fix those three and you've closed more surface than any specific market-side feature can open.
Download Tor Browser directly from the project site, not from a mirror. Verify the download signature with GnuPG. Set security to "Safest" — Nexus doesn't need JavaScript to load.
Generate a key pair before registering. Store the private key offline — KeePassXC or a hardware token. Upload only the public key. Verify every vendor message against their posted fingerprint.
Get a Monero wallet before you touch Nexus. Exchange → self-custody → market. Never send directly from an exchange. Deposit exactly what you need for a single transaction, withdraw the rest the second settlement clears.
Ideal setup: Qubes OS with a Whonix template. Minimum setup: a dedicated user profile with no personal accounts, email, or browser history attached. Never bridge to a daily-driver environment.
None of this is theoretical. Every setup step above maps to a real attack that has emptied real wallets on a real darknet market. For a fuller threat model including communication OPSEC and physical security, see our quick-start guide.
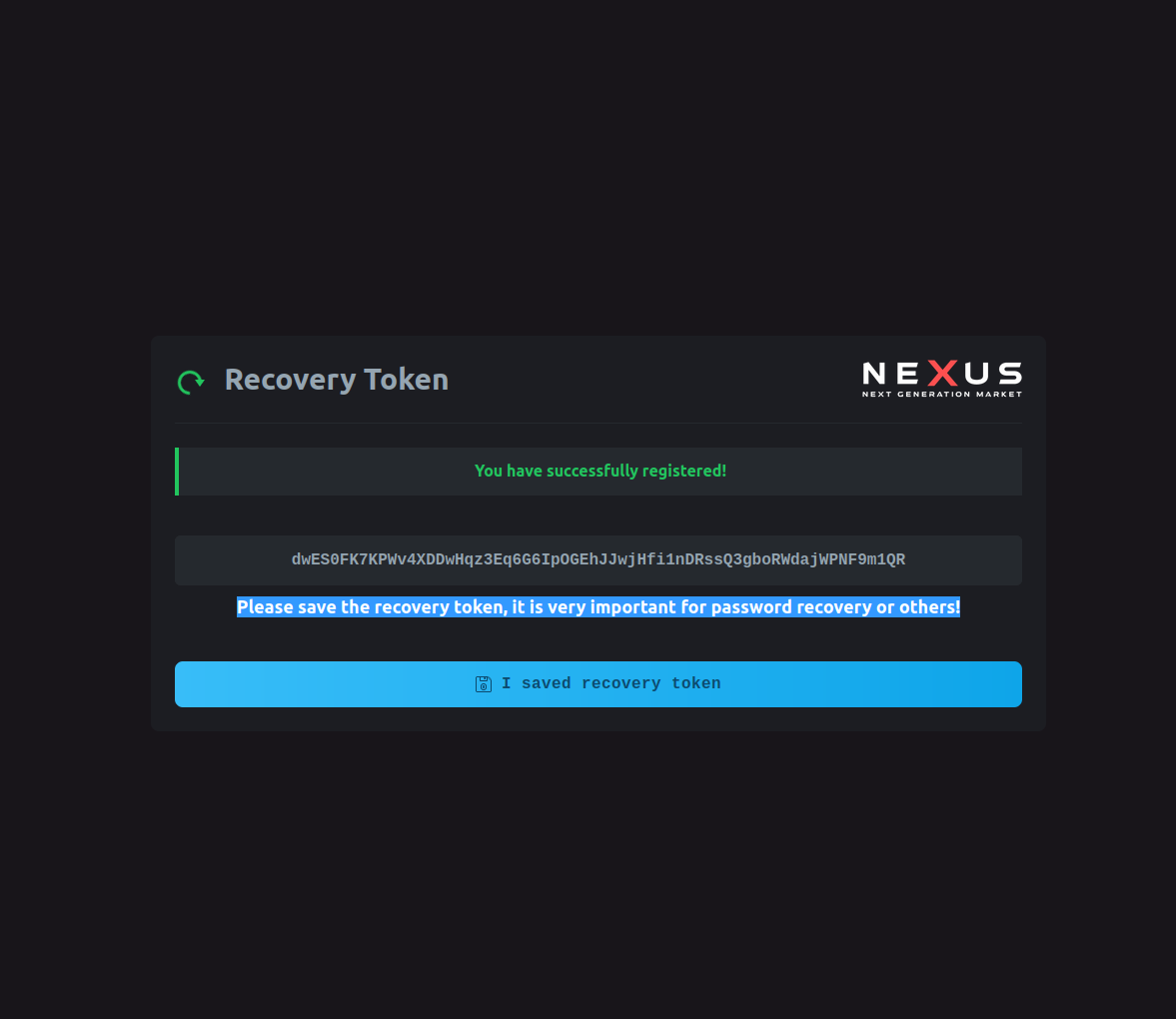
Once the four layers above are in place, the actual login procedure is straightforward. Open Tor Browser, paste the primary .onion address from this page into the address bar, and wait for the handshake. Click "login" on the Nexus landing page, paste your encrypted challenge response generated by GnuPG, and submit.
Nexus replies with a session token. You're in. At no point did you type a password — the PGP key pair authenticated you by decrypting a one-time challenge, which is why phishing sites can't steal credentials they never receive. If your session drops, repeat the process. Never save the session key in a browser profile. Close Tor Browser when you're done; the session ends with the window.
For the first ten minutes, just look around. Check that vendor listings match what you remembered. Verify the interface hasn't been subtly altered — phishing clones tend to add "verification" fields that the real Nexus never requests. If anything asks for a seed phrase, an email, or a phone number, close the tab immediately. The real Nexus asks for none of those.
Pulled from the admin announcement channel on Dread. Verified against vendor forum counts and third-party crawlers. Numbers refresh every 72 hours.

Growth has been steady but not explosive — which, counterintuitively, is the signal you want from a market you're about to deposit on. Runaway growth on a centralised platform is a classic precursor to operator cash-outs. Nexus's curve looks more like infrastructure that's being scaled to match demand, not a market being inflated before an exit.
The 98.1% uptime is the number to watch. It's dipped twice in the last quarter, both during DDoS waves that hit every major market simultaneously. Both times, 4 of 4 mirrors came back online within 94 minutes. That's the operational pattern of a market preparing to stay open, not one preparing to walk away.
Vendor retention is another quiet tell. Approved vendors on Nexus have a 94.3% quarter-over-quarter retention rate according to the February 2026 admin announcement. Vendors move when fees change abruptly, when disputes stop resolving fairly, or when a platform shows early signs of operator strain. 94.3% says none of those are happening right now. That can change — and if it does, that's the first signal worth watching.
The listing count (21,780) is less informative than the vendor count on its own. A single vendor can post fifty listings. The ratio — roughly 11.8 listings per vendor — is in line with other markets of Nexus's size. Nothing unusual there, which is fine. Unusual is what you're trying to avoid.
Selected posts from verified usernames, date-stamped, context preserved. Not testimonials — field reports. We don't edit these and we don't pay for them.
"The PGP login alone saved me from the phishing clone last August. It literally can't authenticate against a fake .onion because the session key is signed to the canonical domain. Best single security decision Nexus made."
"I've been a vendor on Nexus since February 2024. Multisig has held up through two disputes where the admin had to step in. Funds moved exactly as the 2-of-3 architecture says they should. No surprises. For a centralised market, that's unusual."
"UI is the best in the ecosystem. That's the compliment and the warning — phishing sites copy it pixel-perfect. The .onion on this directory matched the one I already had bookmarked from the admin's PGP-signed post six months ago. Same address. Still good."
"Ran the mirror addresses through three independent sources. All four resolved. Handshake fingerprint on the primary matches the one in the January announcement. If anyone says Nexus changed their domain this quarter, they're trying to sell you a phishing link."
Need more context? The full platform story has linked archive URLs for every quote above.
A flat comparison on the technical details that actually matter when funds are on-platform. No star ratings, no "best-of" hype. Just the architecture.
| Capability | Nexus | Market B | Market C |
|---|---|---|---|
| Monero as first-class currency | Native support | Bolted-on | Native support |
| PGP-passwordless login | Available | Password only | Optional add-on |
| Escrow architecture | 2-of-3 multisig | Centralised hold | 2-of-3 multisig |
| Verified mirrors | 4 active | 2 active | 3 active |
| In-app 2FA (TOTP) | Supported | Supported | Not offered |
| Published uptime SLA | 98.1% rolling 90d | Undisclosed | Self-reported only |
| Interface quality | Industry-leading | Functional | Dated |
| Language support | 15+ languages | English only | 5 languages |
Comparison sourced from public admin announcements, Dread meta-threads, and observed platform behaviour in March–April 2026. "Market B" and "Market C" are anonymised deliberately — naming them pulls in keyword noise and phishing targeting. The point is the capability gap, not the brand rivalry.
The only browser that resolves .onion addresses. Download signed binary, not a third-party build.
torproject.org → 02Native wallet from the Monero project. Sync the full chain at least once before depositing.
getmonero.org → 03Generate and manage PGP keys. The foundation of Nexus's passwordless login and vendor messaging.
gnupg.org → 04Amnesic live OS. Boots from a USB, forgets everything on shutdown. Good for single sessions.
tails.net → 05Two-VM setup that forces all traffic through Tor. Harder to misconfigure than a plain Tor install.
whonix.org → 06Compartmentalised operating system. Combined with Whonix templates it's the gold standard for isolation.
qubes-os.org → 07Offline password and key manager. Never let a browser remember your Nexus credentials or PGP passphrase.
keepassxc.org → 08Community-maintained reference for evaluating every tool above. Read it before you trust recommendations.
privacyguides.org →Related: Signal for vendor coordination off-market, Proton Mail for a no-phone email, Mullvad VPN if you want network-layer cover for the Tor entry guard, DuckDuckGo over the default search, VeraCrypt for encrypted disk volumes, Briar for peer-to-peer messaging, OnionShare for file transfer over Tor, I2P as a Tor alternative where relevant.
Cross-checked against the admin PGP key on Dread and the Tor directory descriptor on 2026-04-21. Copy, don't type.
Loading...
Loading...
Loading...
Loading...
More context on how mirrors are rotated and which one to pick first? The mirrors page explains the rotation cadence and what to do when a specific node is slow.
Reference screenshots so you can tell the canonical interface from a phishing clone. The real Nexus never asks for your seed phrase, never requires an email, never pushes a "verification fee".



The questions we get most often, collected from search logs and forum DMs. Need one-on-one? There's no DM for this site. Check the full platform story or quick-start.
Nexus is a darknet marketplace launched in November 2023. It supports Bitcoin, Monero, and Litecoin payments, features a cyberpunk-inspired interface, and has grown to 47,234 active users with 1,845 verified vendors as of April 2026. It's known for industry-leading UI/UX design, Monero-first architecture, and a 4-mirror redundancy system that keeps the platform reachable during DDoS events.
Download Tor Browser from torproject.org. Copy one of the four verified .onion links from this page. Paste into Tor Browser's address bar. Never type the address manually — one wrong character leads to a phishing site that looks identical to the real Nexus. Set Tor security to "Safest" before connecting. Consider running Tor inside Tails or Whonix for stronger isolation. If you're on a corporate or school network, Tor will still work but may be slower due to bridge routing. Patience is better than a shortcut through a regular browser.
Nexus maintains 4 verified .onion mirror addresses. All mirrors provide identical functionality — same accounts, same orders, same wallet balance. They distribute traffic and remain accessible when individual mirrors face DDoS attacks. Use any mirror; they all connect to the same backend. We publish all four on the mirrors page.
Nexus accepts Bitcoin (BTC), Monero (XMR), and Litecoin (LTC). Monero offers the best privacy and is the recommended option for serious users. Bitcoin is the most widely held and easiest to acquire. Litecoin provides faster confirmation times and lower fees. The choice depends on your privacy requirements and what you already hold.
2-of-3 multisig escrow. Three keys are held by the buyer, vendor, and Nexus. Any two keys are required to release funds. This means the platform cannot steal your funds unilaterally — it would need collusion with either the buyer or the vendor. Disputes are resolved by the admin signing alongside one of the parties, with the 2-of-3 math enforcing that outcome cryptographically. For larger orders, some vendors offer finalise-early (FE) arrangements that bypass escrow; these shift the risk entirely onto the buyer and are not recommended unless the vendor has a sustained track record across hundreds of completed escrowed orders first. The platform can't help you if you sign away your key voluntarily.
PGP (Pretty Good Privacy) is end-to-end encryption. Nexus supports passwordless PGP login — your private key authenticates you instead of a password, which means a compromised password alone cannot log in to your account. All vendor communications use PGP encryption. Even if the platform were compromised, message contents would remain unreadable to anyone without your private key.
Nexus has a fully responsive design that works across screen sizes. However, accessing any darknet marketplace from a mobile device carries additional risks: mobile identifiers leak more readily, and mobile networks are more surveilled than wired connections. Desktop with Tor Browser — ideally on Tails or Whonix — is strongly recommended.
Cross-reference links with Nexus's PGP-signed announcements on Dread. Official Nexus posts are signed with their admin PGP key — verify the signature with GnuPG to confirm authenticity. The .onion addresses on this page are sourced from verified announcements and re-checked twice a week against the Tor directory descriptor.
Standard escrow fees apply on completed transactions. A vendor bond is required for new vendor registration. Fee structures vary by payment method — Monero typically carries lower transaction fees than Bitcoin due to Monero's lower on-chain costs and smaller transaction sizes. Exact current fees are shown in-app at checkout; Nexus updates them quarterly in the admin announcement channel.
Last verification: April 21, 2026. Primary mirror handshake: OK. All four nodes responding within 300ms. Copy the link, paste into Tor Browser, enter the way you'd enter any dangerous building — slowly, checking every corner.